In recent years, cyber-attacks have become a significant challenge to the security of the modern state and society. With the rising frequency of malicious actions in cyberspace, followed by billion-dollar losses and damages to the credibility of the targeted entities, governments began to establish strategies, policies, agencies and procedures to defend against cyber-threats. Nevertheless, the perpetrators of cyber-attacks – already considered to be the pirates of the 22nd century – seem to be ahead of both governments and private businesses.
The increasing number of large data thefts, online frauds, or even damage to physical devices caused by malicious software, as well as the disclosures about the role played by cyber-manipulation in influencing political and social processes increase the fears that cyber-attacks may have limitless possibilities to cause harm.
Another worrying trend is the spectacular growth of the ransomware attacks that, according to recent statistics, have been soaring and the number of such incidents increased by 50 percent in 2016.
The growth in the volume of cyber-attacks also indicates that the number of those who engage in damaging actions in cyberspace is increasing. New individuals and groups enter the dark nets of cyberspace, where information about vulnerabilities that provide access to protected systems are traded, the electronic tools to break into safeguarded systems are built and sold (scripts, trojans, worms), and illegal networks are created and leased out to allow large-scale attacks (the so- called botnets). The “Dark Internet” (“darknet”) is now a thriving part of cyberspace, even if it remains largely invisible to the average network user.
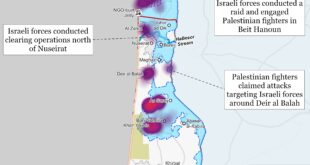
Recent cyber-attacks
Threats recorded by NATO
According to official statistics, NATO warded off 500 cyber-attacks each month in 2016 (an increase of roughly 60% over 2015), with the systems registering over 500 million suspicious cyber events each day. The increasing new cyber threat led to a corresponding reaction and, at the beginning of the year, NATO Secretary General announced at the Davos Forum in Switzerland that the alliance would respond to cyber-attacks in the same way that it would to a conventional assault, making cyber eligible for the invocation of NATO’s mutual defense clause, Article V. In June, NATO included cyber among the official operational domains of warfare, along with air, sea and land. NATO has also named cyber-attacks, along with ballistic missiles and terrorism, as one of the top three threats to the alliance.
NATO officials have said that the alliance already faces daily attacks from a variety of hostile actors, with Russia believed to have the most sophisticated cyber capabilities among NATO’s traditional adversaries. The comments came in the context of the concerns over security following the U.S. intelligence community’s findings that Russia directed cyber attacks against U.S. electoral organizations.
U.S. officials have also warned that Russia may mount similar cyber campaigns against targets in Europe, a warning that was shortly followed by the cyber incidents during the presidential campaign in France and the fake news episode that led to the diplomatic crisis between Saudi Arabia and Qatar.
WannaCry
Last May, the WannaCry malicious software has hit Britain’s National Health Service, some of Spain’s largest companies including Telefónica, the German state railways, as well as computers across Russia, the Ukraine and Taiwan, leading toPCs and data being locked up and held for ransom. The attack affected more than 150 countries.
International investigations led by Britain’s National Cyber Security Centre (NCSC, a subsidiary of GCHQ)) attributed the WannaCry malware to the North Korean-affiliated hacking team known as Lazarus Group. The U.S. National Security Agency also linked the attack to North Korea.
Analyses revealed that an earlier version of WannaCry, named “Wanna Decryptor v1.0”, was being distributed in a way that shared code with an earlier piece of malware called Brambul, which was associated with a North Korean threat group, Nickel Academy (AKA Lazarus group). The code overlap was also seen in another piece of malware used to attack the Polish banking regulator KNF, an operation attributed to the Lazarus group.
WannaCry is not the first ransomware linked to the Lazarus Group and North Korea: a strike against a South Korean supermarket chain was also identified as such. The best-known attack attributed to the Lazarus Group, the 2014 hacking of Sony Pictures, came as the company planned to release the film The Interview, a comedy about journalists embroiled in a plot to assassinate Kim Jong-Un.
Unlike other state actors, such as Russian-affiliated group APT28 (also known as Fancy Bear), many of the Lazarus Group’s activities are based around cyber-crime, with immediate financial reward. Some have speculated that WannaCry may have not been deliberately released: the software contained features that are unusual for advanced ransomware, such as a hardcoded payment address instead of one for each victim, and a universal “killswitch” which prevented the software from self-replicating.
According to intelligence experts on North Korea, the use of ransomware to raise funds for the state would fall under both North Korea’s asymmetric military strategy and ‘self-financing’ policy, and be within the broad operational framework of their intelligence services.
At the beginning of August, nearly three months after the WannaCry ransomware attack, more than £108,000 in bitcoin paid by some of the victims has been withdrawn from the digital wallets the funds were being held in. The money, presumably moved by the hackers, was taken from three bitcoin wallets associated with WannaCry, according to tracking firm Elliptic. Between 24 July and 3 August, more than £18,000 in bitcoin was removed from the three wallets, with the remainder taken out in seven batches worth between £15,000 and £21,000 each. Experts at Elliptic believe the money may be used to purchase goods and services on the dark web, adding another layer of difficulty to tracking the wallets’ owners.
NotPetya and Ukraine
The 27 June NotPetya cyber-attack affected some of the world’s biggest corporate names, including the UK-based advertising group WPP, Danish shipping company AP Moller-Maersk, US delivery service FedEx, food giant Mondelez, Hamburg-based Beiesdorf AG, the maker of Nivea and Labello lip balm, as well as French construction materials company Saint-Gobain and Russian steel and oil firms Evraz and Rosneft.
Technology experts said the attack appeared consistent with an “updated variant” of a virus known as Petya or Petrwrap, a ransomware that locks computer files and forces users to pay a designated sum to regain access. However, analysts at cyber-security firm Kaspersky Labs said they had traced the infections to “a new ransomware that has not been seen before”. According to Kaspersky, the “NotPetya” attack had hit 2,000 users in Russia, Ukraine, Poland, France, Italy, the UK, Germany and the U.S.
Cyber security experts at Symantec said they had confirmed the ransomware in the NotPetya attack was using the same exploit as WannaCry, a program that takes advantage of a software vulnerability. The exploit – called EternalBlue – was leaked by the Shadow Brokers hacker group in April and is thought to have been developed by the U.S. National Security Agency (NSA). To spread within companies that installed the patch to protect themselves against WannaCry, the Petya ransomware appears to have two other ways of spreading rapidly within an organization, by targeting the network’s administrator tools.
The country that was the most severely hit by NotPetya was Ukraine, where the attack affected the government, banks, the state power utility, as well as Kiev’s airport and metro system. The radiation monitoring system at Chernobyl was also taken offline, forcing employees to use hand-held counters to measure levels at the former nuclear plant’s exclusion zone.
Sergiy Demedyuk, head of Ukraine’s ministry of internal affairs’ cyber-crime division, declared that some of the nation’s largest companies were still too scared to share the full scale of the fallout with his investigators. The investigators believe there are aftershocks still to come since the hackers appear to have compromised their targets for some time before they pounced, and might still be sitting on data they could yet exploit.
While NotPetya initially appeared to be a ransomware attack, many in Ukraine suspect its blackmail demands were a cover and, despite denials, there are strong suspicions that the attack, as other cyber-attacks, is part of Russia’s wider efforts to destabilize the country.
According to cyber-security experts, NotPetya was launched in Ukraine using a local software developer’s program, MeDoc that is used by more than 400,000 customers across Ukraine, representing about 90% of its domestic companies. The attackers previously hijacked MeDoc and made it into a remote-control Trojan, after which they launched the attack. According to the police, concrete evidence was obtained that MeDoc was hacked a long time ago and had been used to spy on economic activity within Ukraine. Accordingly, if the perpetrators had, indeed, gathered financial data about most of Ukraine’s companies, it is believed that they might still find ways to cause further damage.
Cyber-security experts estimate that Ukraine might be attacked every six months, with every single business being at risk. They stress that Ukraine is a playground for attacks, most of the companies have already been infected and they should be prepared for the fact that they will be hacked sooner or later.
One of the main targets might be Ukraine’s state-owned energy giant Ukrenergo – also affected by NotPetya. The attacks are believed to come since Ukraine, which, even as an independent country, in the last 25 years used the Russian power grid, recently made an agreement with European electricity transmission operators to modernize its power grid.
Prior to NotPetya, Ukrenergo had been hit by two significant cyber-attacks. In one, a virus was planted and worked in the local network for over one year, collecting information, after which, in December 2016, the hackers put another malware specific for a northern substation and switched it off for 15 minutes. Before that, Ukrenergo was caught up in the Black Energy attack, in December 2015. It took down half a city’s power for three hours in full winter. Consequently, Ukrenergo was prepared to counter the attack and power flowed uninterrupted. However, the company was left without secondary functions for 10 days.
Economic and financial damages
Cyber-risk analysts point out that such attacks were starting to take a greater toll on businesses, since they are no longer limited to data and privacy compromise with expenses incurred to remediate the breach, but they provoke disruption to supply chains and production, material loss of income, and physical damage. Cyber-crime is becoming a main risk for companies, absorbing greater resources and management time. Additionally, the reputational cost of not being able to cope with an attack can be significant, so companies will need to commit appropriate resources to reassure investors.
The growing fight against cyber-attacks has also seen protection spending surge around the world, with the global cyber security market estimated to be worth some £94bn ($120bn) this year – more than 30 times its size just over a decade ago.
Because of the NotPetya attack, the British producer Reckitt Benckiser (which makes, among others, Nurofen, Dettol cleaning products and Durex condoms) is estimated to have lost £100m in revenue, after the attack disrupted production and deliveries of goods to customers in several countries. The cyber-attack’s impact on Reckitt’s operations was both on top line, through disruption to production, order handling and logistics, and margin, through the need to upgrade systems and recover data. Maersk, the world’s largest shipping company, said it had been forced to redirect ships to alternative locations after the attack on its computer systems left it unable to dock and unload containers at some of its ports.
Targeting the critical infrastructure
a) According to a British National Cybersecurity Centre (NCSC) memo disclosed last July, the UK energy sector is likely to have been targeted and probably compromised by nation-state hackers. The NCSC warned that it had spotted connections from multiple IP addresses in the UK infrastructure associated with advanced state-sponsored hostile threat actors, who are known to target the energy and manufacturing sectors. This implies that direct connections are being made between computers in the UK’s energy sector and the attacker’s command-and-control apparatus. Both the Windows data-transfer protocol SMB, and the web backbone HTTP, were used in the connections.
The UK was the third country to note state-sponsored intrusion of its power grid in one week, after reports on fears that Ireland’s Electricity Supply Board was targeted by a group with ties to the Kremlin, and 18 US-based energy companies were sent phishing emails attempting to steal credentials. All the reports appear to be linked, suggesting a widespread campaign to probe energy suppliers for weaknesses and to steal credentials which may prove useful in future attacks.
b) At the end of June, an urgent joint report was issued by the U.S. Department of Homeland Security and the Federal Bureau of Investigation, carrying an urgent “amber warning” (the second-highest rating) for the sensitivity of the threat. It warned that since May, hackers have been penetrating the computer networks of companies that operate nuclear power stations and other energy facilities, as well as manufacturing plants in the United States and other countries. Among the companies targeted was the Wolf Creek Nuclear Operating Corporation, which runs a nuclear power plant near Burlington, Kansas. The Department of Homeland Security has called cyber-attacks on critical infrastructure “one of the most serious national security challenges we must confront.”
The hackers appeared determined to map out computer networks for future attacks, the report concluded. But investigators have not been able to analyze the malicious “payload” of the hackers’ code, which would offer more detail into what they were after.
The origins of the hackers are not known, but the report indicated that an “advanced persistent threat” actor was responsible, which is the language security specialists often use to describe hackers backed by governments. According to cyber-security experts, the hackers’ techniques mimicked those of the organization known as “Energetic Bear”, a Russian hacking group that researchers have tied to attacks on the energy sector since at least 2012.
Hackers wrote highly targeted email messages containing fake résumés for control engineering jobs and sent them to the senior industrial control engineers who maintain broad access to critical industrial control systems, the government report said. The fake résumés were Microsoft Word documents that were laced with malicious code. Once the recipients clicked on those documents, attackers could steal their credentials and proceed to other machines on a network. In some cases, the hackers also compromised legitimate websites that they knew their victims frequented, a technique that security specialists call a “watering hole attack”, and in others, they deployed what are known as “man-in-the-middle” attacks in which they redirected their victims’ internet traffic through their own machines.
Possible origin: NSA cyber-weapons
Both WannaCry and NotPetya attacks were subsequently linked to a previous attack, launched at the end of April against IDT Corporation (International Discount Telecommunications), a U.S. public telecommunications company. The IDT attack used two cyber weapons stockpiled by NSA (National Security Agency) known by the codenames EternalBlue and DoublePulsar that were leaked online in April by a group of hackers calling themselves the Shadow Brokers (alternately believed to be Russia-backed cybercriminals, an NSA mole, or both).
The WannaCry attack, which the NSA and British security researchers tied to North Korea, employed EternalBlue, a tool that took advantage of unpatched Microsoft servers to automatically spread malware from one server to another, so that within 24 hours the hackers had spread their ransomware to more than 200,000 servers around the globe.
The attack on IDT went a step further with DoublePulsar, a tool used by the NSA to penetrate computer systems without tripping security alarms. It allowed NSA spies to inject their tools into the nerve center of a target’s computer system, called the kernel, which manages communications between a computer’s hardware and its software. In IDT’s case, attackers used DoublePulsar to steal an IDT contractor’s credentials. Then they deployed ransomware in what appears to be a cover for their real motive: broader access to IDT’s businesses. The ransom demand was just a smoke screen for a far more invasive attack that stole employee credentials. With those credentials in hand, hackers could have run free through the company’s computer network, taking confidential information or destroying machines.
The attack, which has not been reported at the moment, was not spotted by some of the nation’s leading cyber-security products, the top security engineers at its biggest tech companies, government intelligence analysts or the FBI.
Scans for the two hacking tools used against IDT indicate that tens of thousands of computer systems all over the world have been “backdoored” by the same NSA weapons. Security researchers worry that many of those other infected computers are connected to transportation networks, hospitals, water treatment plants and other utilities.
The IDT cyber security team was able to trace part of the attack to a personal Android phone in Russia and has been feeding its findings to Europol, the European law enforcement agency based in The Hague.
A recent scan on the Internet for the DoublePulsar tool found tens of thousands of host computers infected with the tool, which attackers can use at will. More distressing, the major antivirus products were tested against the DoublePulsar infection and a 99 percent failed to detect it.
In the worst case, attackers could use those back doors to unleash destructive malware into critical infrastructure, tying up rail systems, shutting down hospitals or even paralyzing electrical utilities. The Shadow Brokers resurfaced recently, promising a fresh load of NSA attack tools, even offering to supply them for monthly paying subscribers.
The Shadow Brokers: targeting the NSA
Prior to the last spring incidents, the Shadow Brokers announced in mid-August 2016 that it had published “cyberweapons” that belonged to the NSA on file-sharing sites such as Github. The group said that it would soon hold an auction to sell off a second cache of tools. After a security researcher posted a link to a repository of the supposed NSA software, analysts flocked to the dump. Security researchers quickly discovered that the tools, a collection of malware designed to steal data from their targets, were the real thing. Crucially, The Intercept, a media outlet with access to the NSA files leaked by Edward Snowden, found a sixteen-character string (“ace02468bdf13579”) in the Shadow Brokers’ tools that was referenced in a top-secret, and previously unpublished, NSA manual. The connection proved the provenance of the Shadow Brokers’ find.
Robbing the NSA is not easy. The agency’s elite hacking unit, called Tailored Access Operations (TAO), has an internal network known as the “high side” that is physically segregated from the Internet (the “low side”). Data diodes, devices that allow data to flow one way only, like water from a faucet, make it nearly impossible to hack high-side computers from the low side. When TAO hackers want to attack an adversary, they move their tools from the high side to a server on the low side, navigate through a series of addresses that make their tracks difficult to trace, and install malware on their target. To steal the NSA’s malware, the Shadow Brokers had to compromise a low-side machine that the TAO was using to hack its targets. Some analysts believe that an NSA operator mistakenly uploaded a whole set of tools to a staging computer the hackers were already watching. Another theory was, of course, that of an old-fashioned mole passing on the tools.
Analysts of the case consider that the decision to publish the Shadow Brokers’ coup was triggered by the fact that American investigators had learned that the intruders were using commercial cloud services to “exfiltrate” data out of American corporations and political targets. Cozy Bear, the hacking group believed to be affiliated with the FSB, used some two hundred Microsoft OneDrive accounts to send data from its victims back to Moscow. Data provided by Microsoft also helped America’s elite digital spies identify the DNC intruders “with confidence” as Russian. It is even possible that the U. S. government has been able to identify the names and personal details of individual operators. The Russians knew they’d been caught. On July 30 2016, an FSB press release announced that twenty government and defense organizations had been hit by high-powered spying tools.
Some intelligence analysts also believe that the Shadow Brokers’ publication of the NSA spy kit was a message from one group of professionals to another. Similarly, the announcement of an auction was probably intended as a warning that the hackers were prepared to publish a key that would unlock an encrypted container holding a second batch of stolen tools.
DasCoin: Ponzi scheme with cyber-money
In the financial sector, the cyber-currency Bitcoin’s popularity has grown in the last few years, with nearly twenty-five percent of the American population being familiar with it and more than 1,200 Bitcoin ATMs located worldwide. The main factor of Bitcoin’s success is the block chain technology, a system that helps to ensure that the consumer remains in complete control of their wealth without intermediaries.
While Bitcoin is currently the most widely used digital currency, others have continued to originate from all over the world, but not always for the good of the user.
One example is the so-called DasCoin, which offers new features that aim to surpass Bitcoin in popularity and adoption. Also, DasCoin aims to be one of the few crypto currencies to be accepted by governments around the world, since it is supposedly designed to fully comply with current terrorism financing and anti-money laundering legislation. The team behind DasCoin announced it has partnerships with leading technology providers to integrate DasCoin into the point-of-sale (POS) systems of millions of merchants worldwide. DasCoin also uses a referral-based marketing system which is designed to encourage the development of a global network, willing to recognize, promote and adopt DasCoin.
DasCoin adepts predicted a bright future for DasCoin, which offered major advantages over many of its predecessors and can be used for almost anything. However, several financial analysts warned potential investors and pointed out to some elements that may indicate that DasCoin might be in fact a Ponzi scheme.[1]
DasCoin is operated by a company called Coin Leaders (CL Singapore Pte. Ltd.), which is based in Singapore and is wholly owned by Coin Leadership Limited, based in Dubai. The Chairman of Coin Leaders is John Pretto, who was identified in early to mid-2015 as promoting another Ponzi scheme called OneCoin, presumably based in Bulgaria.
Coin Leaders does not sell products or services, but only a so-called “affiliate membership”. Coin Leaders affiliate membership is tied to an initial investment of between €100 and €25,000 EUR in DasCoin, and, in exchange for their investment, they receive a “software license”. The more funds invested into software licenses, the higher the assigned value to DasCoin. Coin Leaders also pay affiliates a 20% referral fee on funds invested by personally recruited affiliates.
Experts point out to similarities between Coin Leaders’ DasCoin and the previous OneCoin Ponzi-type scheme: affiliates invest in “cycles” (similar to the OneCoin tokens), which are converted into DasCoin (OneCoins), which are assigned an arbitrary value by DasCoin, a centralized authority. DasCoin itself is not publicly tradable and can only be acquired through Coin Leaders investment. Also, besides John Pretto, the Coin Leaders website identifies the CEO of DasCoin Limited as Michael Mathias, another former OneCoin affiliate.
OneCoin had no technological infrastructure, no development, and no white paper. OneCoin met a lot of resistance from various governments all over the world. The London Police is investigating this pyramid scheme and Italy has banned OneCoin activity due to an ongoing fraud investigation.
The Ponzi element of Coin Leaders is the investment of funds which are converted into DasCoins. The value of DasCoin – which is assigned by DasCoin Limited, the company running the point-generation script that spits out DasCoins – is pegged to nothing more than the rate of investment from Coin Leaders affiliates. Affiliates cash DasCoins through Coin Leaders, who use newly invested funds to pay off existing investors, a process that is, in fact, the definition of a Ponzi scheme.
Coin Leaders’ pyramid layer is found in its referral commissions, wherein affiliates are paid to recruit new affiliate investors. Referral commissions are paid out of funds invested by newly recruited affiliates.
As with all Ponzi schemes, once recruitment of new affiliate investors dries up Coin Leaders will collapse. This has already presented itself in OneCoin, amid reports that coin withdrawals by affiliates are next to impossible (the only source of income for most is referral commissions). Currently, an investigation is under way in Poland concerning the DasCoin scheme.
A hackers’ boutique
The dimensions of the phenomenon of cyber-attacks can be judged by the recent uncovering by Kaspersky Lab of an underground hacker boutique forum that offered access to hacked government, corporate, and university servers, often for as little as $6 and $8 apiece.
The trading forum, called xDedic, was essentially renting out space on more than 70,000 hacked servers in 173 countries. The servers offered were Remote Desktop Protocol (RDP) servers, which administrators use to connect to and administer Windows systems on a local network. An attacker with access to an RDP server can connect to other systems, including web servers, often with administrator-level privileges.
Buyers can use the servers as a platform to launch denial-of-service attacks or blast out spam and malware. They can also siphon credit and debit card numbers, confidential email correspondence or other valuable information stored on the systems. Or they can simply use the systems as jumping-off points to compromise other systems on the same network.
The xDedic forum was launched in 2014 and gained popularity when it offered 3,000 compromised servers in mid-2015, and the number grew from there. Of the 70,000 compromised servers the marketplace offered in 2016, more than 6,000 were in Brazil, another 5,000 in China, with Russia coming in not far behind.
The marketplace appears to be operated by Russian-speaking hackers and offers servers to anyone from low-level hackers to nation-state attackers. Hackers breach the servers and provide the credentials to xDedic, which brokers access in return for a cut of the sale price. xDedic has more than 400 sellers, with the most prolific, a seller named UFOSystem, offering more than 16,000 servers for rent.
The owners of xDedic don’t just sell access to hacked servers, they also provide sellers with custom tools to help them compromise servers, including a SysScan tool that automatically collects information about compromised systems, such as the web sites that can be accessed from them, the amount of memory on the systems and any software installed on them. Interested buyers can shop xDedic for the server that best meets their needs based on geographical location, configuration, memory, and other features. In addition to the SysScan tool, the marketplace owners also provide hackers with a tool to reconfigure the servers they compromise to help hide their presence on the systems and prevent the real system administrators from kicking them out.
Vulnerabilities of the Cyber Societies
The increasing rate, scope and destructiveness of the cyber-attacks is favored, according to most sociologists, by the social and behavioral changes that the Internet and, more recently, the social media brought to human society.
According to most estimates, 95 percent of all information existing in the planet is digitized and most of it is accessible on the Internet and other computer networks. Recent estimates reveal that, by 2025, the accumulation of data worldwide will equal that of one trillion libraries, each containing 60,000 copies of Lev Tolstoy’s War and Peace, or a digital playlist lasting 326 billion years.
Personal and commercial interactions are increasingly moving online, and all of that information is being collected and catalogued. Networked sensors can now monitor and collect data about almost anything from almost anywhere. And rapidly falling digital-storage costs have made it easier to build detailed records of personal behavior, consumer habits, and industrial operations. The transformation of industry has been even more breathtaking, as the “Internet of Things” has expanded from toothbrushes and refrigerators to airplanes and drilling equipment.
Internet is a technology of freedom, originally financed by the Pentagon and later used by scientists, engineers, and their students, with no direct military application in mind. The expansion of the Internet from the mid-1990s onward resulted from the combination of three main factors:
- The technological discovery of the World Wide Web by Tim Berners-Lee and his willingness to distribute the source code to improve it by the open-source contribution of a global community of users, in continuity with the openness of the TCP/IP Internet protocols. The web keeps running under the same principle of open source and two-thirds of web servers are operated by Apache, an open-source server program.
- Institutional change in the management of the Internet, keeping it under the loose management of the global Internet community, privatizing it, and allowing both commercial and cooperative uses.
- Major changes in social structure, culture, and social behavior: networking as a prevalent organizational form; individuation as the main orientation of social behavior; and the culture of autonomy as the culture of the network society.Social Network Sites are defined as web-based services that allow individuals to (1) construct a public or semi-public profile within a bounded system, (2) articulate a list of other users with whom they share a connection, and (3) view and traverse their list of connections and those made by others within the system.Nearly 60 percent of adults in the U.S. have at least one SNS profile, 30 percent two, and 15 percent three or more. The most important activity on the Internet at this point in time goes through social networking, and SNS have become the chosen platforms for all kind of activities, not just personal friendships or chatting, but for marketing, e-commerce, education, cultural creativity, media and entertainment distribution, health applications, and socio-political activism.Government and military computer systems are commonly attacked by activists, as well as foreign powers. Local and regional government infrastructure such as police and intelligence agency communications, personnel records, student records, and financial systems are also potential targets as they are now all largely computerized. Passports and government ID cards that control access to restricted facilities can be vulnerable to cloning.Large corporations are common targets, for financial gain through identity theft. Medical records have also been targeted for use in identify theft, health insurance fraud, and impersonating patients to obtain prescription drugs for recreational purposes or resale. The aviation is also reliant on a series of complex system which could be attacked. A simple power outage at one airport can cause repercussions worldwide, much of the system relies on radio transmissions which could be disrupted, and controlling aircraft over oceans is especially dangerous because radar surveillance only extends 175 to 225 miles offshore. There is also potential for attack from within an aircraft. The consequences of a successful attack range from loss of confidentiality to loss of system integrity, air traffic control outages, loss of aircraft, and even loss of life.Many consumer devices, beginning with the desktop computers and laptops are commonly targeted to gather passwords or financial account information, or to construct a botnet to attack another target. Smart phones, tablets, smart watches and other mobile devices can be exploited, and may collect personal information, including sensitive health information. Wi-Fi, Bluetooth, and cell phone networks on any of these devices could be used as attack vectors, and sensors might be remotely activated after a successful breach. Medical devices have either been successfully attacked or had potentially deadly vulnerabilities demonstrated. There are many reports of hospitals and hospital organizations getting hacked, including ransomware attacks, viruses and data breaches of sensitive data stored on hospital servers.The typical victims of this new kind of attack are carefully chosen government agencies and leading industrial companies, rather than random individuals. The driving logic behind the malicious activity is reversed: it is not the number of victims that ensures success, but rather the depth and complexity of the attack pointed at a very narrow group of targets that brings results. This may suggest that the true goal of the attacks is a desire to acquire sensitive information, so the question of who is behind those attacks can be answered only by deducing “who benefits.” Since these operations are driven by the demand for specific data, most likely it is the adversaries of the targeted states or corporations that are behind such attacks.Cyber-security experts often talk about the level of exposure, or the amount of “attack surface,” when describing security vulnerabilities and cyber risks. Both factors affect the likelihood that an individual or organization will fall victim to either widespread internet threats, such as WannaCry, or to more targeted threats, such as government surveillance.NEI researchers define “exposure” as either natively unencrypted services on the public internet or services available via the public internet that are unsuitable for widespread accessibility. If one or both conditions are found to be true for Internet Protocol (IP)-accessible servers, then it counts against the country and increases its overall exposure rating. According to the 2017 NEI, the countries of Zimbabwe, Hong Kong Special Administrative Region, Samoa, Republic of the Congo, Tajikistan, Romania, Ireland, Lithuania, Australia and Estonia top the list. China and Russia fall into the top 50 most exposed, but given its large Internet Protocol version 4 (IPv4) address space, the U.S. ranks relatively low in total exposure, researchers reported.- Another recent report on vulnerabilities was issued by the U.S. Institute for Critical Infrastructure Technology (ICIT) and titled “Metadata: the Most Potent Weapon in this Cyber-war”, stressed the threats posed by the so-called “weaponized metadata” and the risks that are increasing because of growth in the collection, aggregation and sale of end users’ internet metadata, as well as users’ preference profiles and browser histories.Armed with detailed knowledge of who victims are and how they behave online, threat actors can conduct a variety of cyber-enabled attacks, from social-engineering techniques such as spear phishing to “psychographic and demographic Big Data algorithms” employed to push “fake news.” The report provides case studies on how metadata could be used to target anyone, from executives to entry-level employees, in specific critical infrastructure sectors, such as energy, finance and healthcare. Threat actors can use victims’ browsing patterns to plan social-engineering campaigns, precision target propaganda, plant watering-hole sites, etc.In combination with the detailed demographic and psychographic information contained in stolen forms used by individuals to apply for government security clearances, the threat actors could identify with pinpoint accuracy individuals who are susceptible to counterintelligence operations, along with effective methods for compromising each one. The ICIT report notes that browsing histories that reveal frequent visits to gambling sites, multiple credit card pages, loan applications or even dating sites could indicate that a person is ripe for financial blackmail or transformation into an intelligence asset.Mass self-communications and virtual communitiesThe transformation of communication from mass communication to mass self-communication has contributed decisively to alter the process of social change. As power relationships have always been based on the control of communication and information that feed the neural networks constitutive of the human mind, the rise of horizontal networks of communication has created a new landscape of social and political change by the process of disintermediation of the government and corporate controls over communication.Networked social movements have been particularly active since 2010, and especially in the Arab revolutions; in Europe and the U.S. as forms of protest against the management of the financial crisis; in Brazil; in Turkey; in Mexico; and in highly diverse institutional contexts and economic conditions. The similarity of the movements in extremely different contexts makes them a pattern for the social movements that are characteristic of the global network society. In all cases one observes the capacity of these movements for self-organization, without a central leadership, on the basis of a spontaneous emotional movement. In all cases there is a connection between Internet-based communication, mobile networks, and the mass media in different forms, feeding into each other and amplifying the movement locally and globally.The use of the Internet and the so
cial networking sites are at the origin of the so-called online or virtual communities, which are seen as beginning to represent a new form of human communal existence, providing new scope for building a shared experience of human interaction. On the other hand, while instant communication means fast access, it also means that information is posted without being reviewed for correctness. It is difficult to choose reliable sources because there is no editor who reviews each post and makes sure it is up to a certain degree of quality. This opens possibilities for media and mass manipulation bigger than anything in recent history.The cyber-attacks in 2015 and 2016 against the U.S. Democratic National Committee (DNC) and other cyber-operations through which, according to the U.S. intelligence services and cyber-security firms, Russia aimed to influence the American electoral process are but a recent example of the power of “weaponized information” and “fake news” to manipulate a public opinion that came to depend almost exclusively on the social network services.The reports, part of the Oxford Internet Institute’s Computational Propaganda Research Project, cover nine nations, including Brazil, Canada, China, Germany, Poland, Ukraine and the United States. In a 2017 report, Facebook publicly stated that its site has been exploited by governments for the manipulation of public opinion in other countries – including during the presidential elections in the U.S. and France. It identified three main components involved in an information operations campaign: targeted data collection, content creation and false amplification and includes stealing and exposing information that’s not public; spreading stories, false or real, to third parties through fake accounts; and fake accounts being coordinated to manipulate political discussion, such as amplifying some voices while repressing others.At one point, the account boasted as many at 150,000 followers, and, according to other Twitter users, was connected to similar accounts, which experts say suggests a network created to disseminate propaganda.Social media manipulation: the power of the botsResearchers at USC used more than one thousand features to identify bot accounts on Twitter, in categories including friends, tweet content and sentiment, and time between tweets. Using that framework, researchers’ estimates suggested that between 9% and 15% of active Twitter accounts are bots. However, the researchers stressed that complex bots could have shown up as humans in their model, making even the 15% figure a conservative estimate.While USC’s researchers highlighted the benefits of some bots, which perform useful functions, such as dissemination of news and publications, they pointed to the downside of bots, mentioning a growing record of malicious applications of social bots. “Some emulate human behavior to manufacture fake grassroots political support… [and] promote terrorist propaganda and recruitment.”While there is evidence of institutional support for the use of bots, for example by party campaign managers, bots also massively multiply the ability of one person to attempt to manipulate people.While Russian propaganda on social media is better known for its external successes, including allegations of state involvement in the U.S. and French presidential elections, Russia’s social media is also heavily infiltrated with digital propaganda. Researchers noted that Russia first developed its digital propaganda expertise for dealing with internal threats to stability and drowning out dissent to Putin’s regime while providing an illusion of overwhelming consensus. The online propaganda tools thus created were later deployed in foreign operations, with the main “testing ground” for them being Ukraine.In Internet slang, a “troll” [2] is a person who sows discord on the Internet by starting arguments or upsetting people, by posting inflammatory or off-topic messages in an online community with the intent of provoking readers into an emotional response or of otherwise disrupting normal, on-topic discussion. When interacting with each other, trolls often share misleading information that contributes to the fake news circulated on sites like Twitter and Facebook. As with all professional media systems, pro-Russia online disinformation is designed to meet the needs of as many different target audiences as possible. The primary target group for the St. Petersburg troll factory seems to be ordinary citizens, but politicians and other public figures are targeted as well. Spreading disinformation online is cheap compared to television or print methods. On Facebook, people’s need to belong to a community is taken advantage of. Troll group administrators manipulate group members to accept their agenda by bullying or blocking all who oppose the leaders. Members’ comments that support the leaders’ agenda are encouraged by positive feedback from the administrators (‘likes’ and similar-minded comments). The only option for a troll group member is to accept administrators’ views or face being left out. Members are tricked into believing that the offensive language used is a ‘normal use of free speech’.Fake News: “more real” than real newsIn the 21st century, the capacity to mislead was enhanced by the widespread use of social media. One of the websites that enabled fake news’ proliferation was the Facebook Newsfeed. In late 2016, fake news gained notoriety following the uptick in news content by this means, and its prevalence on Twitter. In the United States, 62% of Americans use social media to receive news.Researchers identified the following types of fake news: - Fake news also undermines serious media coverage and makes it more difficult for journalists to cover significant news stories. An analysis found that the top 20 fake news stories about the 2016 U.S. presidential elections received more engagement on Facebook than the top 20 news stories on the election from 19 major media outlets.
- Fake newsconsists of deliberate misinformation spread via traditional print and broadcast news media or online social media. It is written and published with the intent to mislead in order to gain financially or politically, often with sensationalist, exaggerated, or patently false headlines that grab attention. Fake news often employs eye-catching headlines or entirely fabricated news stories to increase readership, online sharing and Internet click revenue.
- Pro-Kremlin disinformation material is first published on unreliable and non-journalistic media, including Russian state media websites, Vkontakte, YouTube, Twitter, Facebook, blogs and special websites. Comments without links are also posted straight to forums, and each troll has to produce hundreds of comments during a 12-hour shift. More visually oriented people are lured in with memes, caricatures and videos.
- The power of the “trolls” was first put to use in Russia, after the Kremlin defined, in 2000, ‘information security’ as the protection of Russia’s national interests in the information sphere and Russian Defense Minister Sergei Shoigu called the media a ‘weapon’. Consequently, in recent years the Russian state’s information warfare capabilities have developed rapidly to match the evolution of the social media, and a significant part of the new activities is represented by the ‘trolls’, recruited commentators who distribute the messages of Russia’s political leaders online. Developed first in Russia, the “trolls” were soon “adopted” by other nations and groups interested in shaping public opinion.
- Enter the ‘trolls”
- In Russia, the studies estimate that around 45% of highly active Twitter accounts are bots (not personal but automatically operated accounts).
- Some of the simpler techniques include bots to like, share and post on the social networks. Such accounts can serve to drown out real debate between humans and they can simply make online measures of support, such as the number of likes, look larger – crucial in creating the illusion of popularity. Such a process is called “manufacturing consensus” – creating the illusion of popularity so that a political candidate can have viability where they might not have had it before. The illusion of online support for a candidate can spur actual support through a bandwagon effect.
- Since Twitter currently has 319 million monthly active users that results in nearly 48 million bot accounts, using USC’s high-end estimate.
- According to recent research from the University of Southern California (USC) and Indiana University, up to 15 percent of the Twitter accounts are in fact bots (machines impersonating as human users of the social networks) rather than people.
- It was promptly suspended by Twitter, but the incident was a significant, if not singular, example of the window provided by the social media, not just for Russia, but for any adversary to influence or discredit political personalities.
- A recent example of the effects of the social media manipulation came from a leading politician in the U.S., who tweeted to his 35 million followers his gratitude to a social-media “super fan”. According to experts, the super fan’s account was in fact a Russian bot – a fake Twitter account pretending to represent a real person and created to influence public opinion or promote a particular agenda – part of a Russian-backed sophisticated disinformation campaign to exacerbate disputes in American politics.
- Internet manipulation (the media manipulation on the Internet) may be conducted for purposes of propaganda, discrediting, harming corporate or political competitors, improving personal or brand reputation or plain trolling. To accomplish such objectives, online influencers, hired professionals and/or specific software (Internet bots) may be used. Cognitive hacking is a cyber-attack that aims to change users’ perceptions and corresponding behaviors.
- According to a recently released set of studies from the University of Oxford, propaganda on social media is increasingly being used to manipulate public opinion around the world, and everyday-used social media is quickly becoming an international battleground for dirty politics.
- Internet manipulation and cyber-war in politics
- Online communities of various kinds (social networking sites, blogs, media sharing sites, etc.) are posing new challenges for all levels of law enforcement in combating many kinds of crimes including harassment, identity theft, copyright infringement, etc. Laws governing online behavior pose another challenge to lawmakers in that they must work to enact laws that protect the public without infringing upon their rights to free speech.
- New forms of civic engagement and citizenship have emerged from the rise of social networking sites. Networking sites act as a medium for expression and discourse about issues in specific user communities. Online content-sharing sites have made it easy for youth as well as others to not only express themselves and their ideas through digital media, but also connect with large networked communities. Within these spaces, young people are pushing the boundaries of traditional forms of engagement such as voting and joining political organizations and creating their own ways to discuss, connect, and act in their communities.
- In the first decade of the 21st century, many social movements around the world have used the Internet as their space of formation and permanent connectivity, among the movements and with society at large. These networked social movements, formed in the social networking sites on the Internet, have mobilized in the urban space and in the institutional space, inducing new forms of social movements that are the main actors of social change in the network society.
- The power relations, the relations that constitute the foundation of all societies, as well as the processes challenging institutionalized power relations, are now shaped and decided in the communication field. Over the last four decades the advent of the Internet and of wireless communication has shifted the communication process in society at large from mass communication to mass self-communication. This is from a message sent from one to many with little interactivity to a system based on messages from many to many, multimodal, in chosen time, and with interactivity, so that senders are receivers and receivers are senders.
- The report mentioned the healthcare sector, followed closely by energy and finance, as the most vulnerable critical infrastructure sectors.
- The report gives an extended example of how China could use metadata for counterintelligence operations, with potentially serious consequences to national security. Under the current relaxed data privacy rules in the U.S., a state-owned Chinese business (most likely a shell company) could buy metadata on U.S. consumers in bulk from a U.S. ISP. Chinese intelligence agents could then combine the metadata with data stolen by the Chinese APT threat actor Deep Panda in the 2015 Office of Personnel Management (OPM) breach. Using artificial intelligence, Chinese agents could then de-anonymize the internet metadata and correlate it to workers in critical infrastructure sectors.
- The ICIT report notes that metadata can be descriptive (e.g., identification details), structural (e.g., combination and container details) or administrative (e.g., creation, technical and access details). Examples of internet metadata include the title, sender and receiver of emails, the unique identification number (i.e., International Mobile Equipment Identity, or IMEI) of mobile devices and the duration of users’ visits to websites. These examples are just a few of the dozens of data types that contextualize users’ online behavior.
- The 2017 NEI’s other key findings included over 1 million endpoints globally that currently expose Microsoft file-sharing services (SMB, TCP port 445). Of those 1 million, 800,000 were confirmed to be Windows systems, “spanning virtually the entire product and release version lineage of the company,” the researchers wrote. SMB exposure is significant because the WannaCry cyber-attack exploited a vulnerability in the SMB protocol which has long concerned security researchers.
- A recent report issued by the cyber-security company Rapid7 gathered data for its 2017 National Exposure Index (NEI), which investigates “risk of passive eavesdropping and active attack on the internet,” providing “measurable, quantitative answer to the nature of internet exposure and where, physically, those exposed services are located.”
- Cyber risk and metadata vulnerabilities
- A distinctive category of cyber-threats are so called targeted attacks, which are aimed at stealing sensitive data from a selected group of internet users, or even a precisely defined single user (e.g., a global corporation or a government agency).
- In the case of the network of physical objects such as devices, vehicles, and buildings that are embedded with computerized devices that enables them to collect and exchange data – the Internet of Things (IoT) – cyber-attacks are likely to become an increasingly physical (rather than simply virtual) threat. If a front door’s lock is connected to the Internet, and can be locked/unlocked from a phone, then a criminal could enter the home at the press of a button from a stolen or hacked phone. People could stand to lose much more than their credit card numbers in a world controlled by IoT-enabled devices.
- Vehicles are increasingly computerized, and connected cars may use Wi-Fi and Bluetooth to communicate with onboard consumer devices and the cell phone network. Self-driving cars are expected to be even more complex. All of these systems carry security risks, such as malicious CD being used as an attack vector, and the car’s onboard microphones being used for eavesdropping. If access is gained to a car’s internal control system, the danger is much greater (in a 2015 test, hackers remotely carjacked a vehicle from 10 miles away).
- Computers control functions at many utilities, including telecommunications, the power grid and opening/closing valves in water and gas networks. The Internet is a potential attack vector for such machines if connected.
- In the financial sector, web sites and apps that store credit card numbers, brokerage and bank account information are prominent hacking targets, because of the potential for immediate financial gain from transferring money, making purchases, or selling the information on the black market. In-store payment systems and ATMs are tampered with in order to gather customer account data and PINs.
- The growing number of computer systems and the increasing reliance upon them of individuals, businesses, industries and governments means that there are an increasing number of systems at risk, in all the domains of economic and social life.
- Social networking uses, in time globally spent, surpassed e-mail in November 2007. It surpassed e-mail in number of users in July 2009. In terms of users it reached 1 billion by September 2010, with Facebook accounting for about half of it. In 2013 it has almost doubled, particularly because of increasing use in China, India, and Latin America. There is a great diversity of social networking sites (SNS) by countries and cultures. Facebook, started for Harvard-only members in 2004, is present in most of the world, but QQ, Cyworld, and Baidu dominate in China; Orkut in Brazil; Mixi in Japan; etc.
- Since 2002 (creation of Friendster, prior to Facebook) a new socio-technical revolution has taken place on the Internet: the rise of social network sites where all human activities are present, from personal interaction to business, work, culture, communication, social movements, and politics.
- satire or parody (no intention to cause harm but has potential to fool)
- false connection (when headlines, visuals of captions don’t support the content)
- misleading content (misleading use of information to frame an issue or an individual)
- false content (when genuine content is shared with false contextual information)
- imposter content (when genuine sources are impersonated with false, made-up sources)
- manipulated content (when genuine information or imagery is manipulated to deceive, as with a doctored photo)
- fabricated content (new content is 100% false, designed to deceive and do harm)Ukraine: a testing field for hybrid warfareHybrid warfare is Russia’s modern interpretation of a Soviet military doctrine called “deep battle,” in which military operations extend beyond the front lines deep into an enemy country’s territory in order to hinder its ability to wage war. Whether it is Ukraine, the EU, or the United States, Russia has the same playbook and goals. It employs hybrid warfare: fake news, computer hacking, cyber-attacks on critical infrastructure, snap drills, direct military interventions.The war in Ukraine has become a proving ground for Russia’s strategic use of hybrid warfare weapons like propaganda and cyber-attacks, with examples of digital conflict seen across the spectrum, in every domain, from politics to diplomacy, in military operations, business, critical infrastructure, and social media. Russian cyber- attacks have targeted Ukraine’s power grid, its biggest international airport and the country’s 2014 presidential election. And Russian propaganda has targeted the morale of Ukrainian civilians and soldiers. The systematic strikes and protests, which result in destabilizing the socioeconomic and the legal system of the country, are considered to be a direct result of Russian propaganda.Manipulation: much cheaper than campaigningThe analysis of Chinese, Russian, Middle Eastern, and English-based fake news services found that these options offer a cost-effective alternative to traditional advertising and promotional efforts, often by manipulating social networks to spread dubious content.A key ingredient, the report noted, is “fake news fabricated as truth that panders to its audience’s ideologies and promises an illusion of the future – enough to compel people to join an imagined cause”.Buying reposts and biased comments on its content can boost the campaign. Some of these networks will also distribute real news, allowing the sites to build a reputation and blur the line between propaganda and legitimate content. In total, a yearlong campaign with a $400,000 budget should be able to “manipulate a decisive course of action”, the research found.Case study: Internet manipulation and the U.S. electoral processHacking of the elections systemsA report issued in the same context by the Institute for Critical Infrastructure Technology (ICIT) and titled “The Painfully Vulnerable Election System and Rampant Security Theater” details at least 20 different vulnerabilities that could provide hackers entry into state voting systems, with the authors noting that none of the threats they discussed could be considered new or novel to even amateur hackers.If focused on the so-called “swing regions” (where the voting preferences are more balanced), and using stealth and sophistication, it is possible for a dedicated APT to influence a national election.Russian services have a 20-year tradition of hacking the United States. In 1996, five years after the end of the USSR, the Pentagon began to detect high-volume network breaches from Russia. The campaign was an intelligence-gathering operation: whenever the intruders from Moscow found their way into a U.S. government computer, they binged, stealing copies of every file they could. By 1998, when the FBI code-named the hacking campaign Moonlight Maze, the Russians were commandeering foreign computers and using them as staging hubs. At a time when a 56 kbps dial-up connection was more than sufficient to get the best of Pets.com and AltaVista, Russian operators extracted several gigabytes of data from a U. S. Navy computer in a single session. With the unwitting help of proxy machines – including a Navy supercomputer in Virginia Beach, a server at a London nonprofit, and a computer lab at a public library in Colorado – that accomplishment was repeated hundreds of times over. Eventually, the Russians stole the equivalent, as an Air Intelligence Agency estimate later had it, of “a stack of printed copier paper three times the height of the Washington Monument.”This sort of espionage was a continuation of the cold war, when both the USSR and the United States subtly, and sometimes covertly, interfered with foreign elections. The new feature in the DNC case, for the first time, Russia used a hacking operation that collected massive quantities of stolen information, to meddle in an American presidential election through a classic cocktail of fact and fabrication that the Russians call kompromat, for ‘compromising material.’The Democratic National Committee (DNC) cyber-attacksCrowdStrike was soon able to reconstruct the hacks and identify the hackers. One of the groups, known to the firm as Cozy Bear, had been rummaging around the DNC since the previous summer. The other, known as Fancy Bear, had broken in later on. While security researchers had long suspected that both groups were directed by the Russian government, each of the attackers seemed unaware of what the other was doing. On June 14 2016, CrowdStrike posted a report that detailed the methods used by the intruders and named the Russian spy agencies it believed responsible for the hack. Fancy Bear, the firm said, worked in a way that suggested affiliation with the GRU. Cozy Bear was linked to the FSB.“Campaigning” from MacedoniaThese sites open a window into the economic incentives behind producing misinformation specifically for the wealthiest advertising markets and specifically for Facebook, the world’s largest social network, as well as within online advertising networks such as Google AdSense. The operators know that the info in the blogs is bad, false, and misleading but the rationale is that ‘if it gets the people to click on it and engage, then use it’, since it is an easy way to make money. The Macedonians see a story elsewhere, write a sensationalized headline, and quickly post it to their site. Then they share it on Facebook to try and generate traffic. The more people who click through from Facebook, the more money they earn from ads on their website.Four of the five most successful posts from the Macedonian sites were found to be false.In the first week of August, a virtual army of accounts identified as having ties to the Russia-backed disinformation campaigns targeting the US political system zeroed in on efforts to attack national security adviser H.R. McMaster.Researchers said the fake accounts sometimes disseminate content from well-known Russian-backed sources including Sputnik or RT, which are then picked up by U.S. politicians, or they might amplify content created by media outlets known for misinformation.The importance of the social media services for the Russian cyber-war against the U.S. was revealed in another case, announced at the beginning of March 2017, when the Department of Justice charged two members of the Russian Federal Security Service (FSB) and two hackers-for-hire for allegedly breaching Yahoo’s servers. Prosecutors believe the FSB agents carried out the hack in their capacity as Russian government officials and the Justice Department called it the largest data breach in US history. Prosecutors said that the hackers’ access to 30 million Yahoo accounts was used in order to set up an automated system to steal those users’ contacts. These contacts lists are highly valuable to spammers, as someone is much more likely to click on some malicious spam link if it appears to come from a friend of colleague.The hackers are accused of using all kinds of methods, from simple things like “spear phishing” to stealing and creating their own authentication cookies from Yahoo’s servers. Spear phishing, works by sending someone an email that looks authentic, like a password reset email that appears to be sent from Google. In reality, the email contains a malicious link that tricks one into giving one’s password to a hacker or secretly installing malware onto the computer.Countering the Internet manipulation: between censorship and free speechHowever, som
e steps are beginning to be taken. European and American regulators have tried to align their rules on data sharing in certain areas, such as counterterrorism. In 2016, the US and the EU concluded an “Umbrella Agreement,” which establishes a framework for protecting data exchanged in the process of criminal investigations.The key enablers and thus the potential solvers of the Internet manipulation problem are seen to be the international social media companies, mainly Facebook and Twitter. Both provide harassers and propagandists with a platform, but leave crimes for the victims and local police to tackle. Making user reports about hate speech does not currently help much, as Facebook replies to many such reports with the automatic reply ‘user/content is not breaking the community standards’.However, the big social media firms show an apparent disinterest in how their networks were being used. Facebook, for instance, leaves most of its anti-propaganda work to external organizations such as Snopes and the Associated Press, who operate semi-autonomous fact-checking teams aimed at marking viral news stories as true or false while Twitter’s anti-bot systems are effective at fighting commercial activity on the site, but seem less able or willing to take down automated accounts engaging in political activity.Advances in Germany and Italy In the context of the future elections for the Bundestag, in autumn 2017, Germany plans to implement stricter control of social media. Already, social networks see high activity among extremist movements and radical parties, according to the organization Jugendschutz, which monitors online political extremism and criminal content, especially among youth. To counter such threats, the Federal Ministry of the Interior developed a new cyber-security strategy. In addition to improvements to existing cyber-defense techniques, it wants to establish mobile rapid-reaction forces within the Federal Office for Security in Information Technologies (BSI), federal police, intelligence and counterintelligence agencies. A special unit composed of IT experts will be formed to be able to carry out a counterattack on foreign servers if needed.Representatives of all parties in the Bundestag declared that during the campaign they would not use fake news and manipulated information in their campaigns, and the Christian Democratic Union said it intends to create a rapid-response team to counter false information online.However, some things remain out of control, especially activities from the “outside,” particularly from Russia. After the 2015 hack of the Bundestag’s computer network many expect that the stolen, confidential information will be made public during the campaign. A cyber “Geneva Convention” - After the recent WannaCry and NotPetya attacks, the call for a cyber Geneva Convention launched by Microsoft has renewed, gaining the interest and support, among others, of Deutsche Telekom. The support of an international company has sparked consideration on an intergovernmental level for a treaty covering all cyber-attacks.
- – In Italy, a bill was introduced aimed at “preventing the manipulation of online information” with fines of up to EUR 5,000 for “non-journalistic” websites, social media etc. that publish or disseminate “fake, exaggerated or tendentious news regarding data or facts that are manifestly false or unproven.” Creating or disseminating “rumors or fake, exaggerated or tendentious news that may provoke public alarm or acts in such a way as to damage public interests or mislead the public opinion” is punishable with up to 1 year in prison.
- In the case of the social media, at the end of 2015 the German government also reached agreement with social media platforms on control of content. Under the deal, punishable postings are to be removed within 24 hours. In August 2016 alone, Facebook removed about 100,000 posts containing hate speech, and the head of the Social Democratic Party, Thomas Oppermann, suggested introducing financial penalties on the owners of social media platforms of up to €500,000 for failing to remove false information or comments inciting hate within 24 hours.
- Interior Minister Thomas de Maiziere also announced a plan to set up a centre under the Federal Press Office to fight misinformation and combat false information on the internet. Christian Democratic politicians also proposed legislation allowing for the prosecution of disinformation that aims to “destabilize the country.”
- While the legal restrictions on freedom of expression in Germany are stricter than in the U.S. – with punishment from 3 months to 5 years for anyone inciting hatred against another person or group of people on the grounds of nationality, origin, ethnicity, religion or calls for violence, including in internet activity – there is no legal framework to deal with disinformation, fake news or use of social bots.
- – In Germany, fear of online destabilization has led to the proposal and implementation of world-leading laws requiring social networks to take responsibility for what gets posted on their sites. Currently, Germany leads the way as a cautionary authority over computational propaganda, seeking to prevent online manipulation of opinion, although some of the measures lack legitimacy and suitable enforcement, and some are seen as disproportionate responses considering their implications for freedom of expression.
- For the most part, they leave it to the user community to police themselves, and flag accounts, while social networks tend to comply only with the minimum legal requirements.
- Both Facebook and Twitter need to start ‘cleaning up’ the fake profiles that are coordinating nasty operations against citizens. At the moment, an individual user is quite helpless against an orchestrated hate campaign. The same applies to YouTube, which provides a platform for propaganda videos and hate speech.
- The role of the social media operators
- Although events in recent years have underscored the threat of data breaches, as well as of Internet manipulation, lawmakers and regulators still display a surprising lack of understanding about the technologies used to gather, transfer, and store data. An example is the proliferation of “localization” rules requiring that a country’s data be stored within its own borders. Such measures, while well-meaning, are, in fact, the digital equivalent of hiding one’s cash under the mattress. The process of tailoring software enabling data storage and protection to individual jurisdictions can be self-defeating, to the extent that it introduces new vulnerabilities for hackers to exploit. Moreover, when countries enact complex and divergent data rules, local citizens and businesses bear the costs of compliance, giving the (mostly American) technology giants a further advantage.
- According to the indictment, the hackers installed malware in order to further compromise Yahoo’s severs and to cover up their tracks once they gained access.
- In addition, the hackers were accused of targeting users affiliated with U.S. online service providers, including but not limited to webmail providers and cloud computing companies, whose account contents could facilitate unauthorized access to other victim accounts; Russian journalists and politicians critical of the Russian government; Russian citizens and government officials; former officials from countries bordering Russia; and U.S. government officials, including cyber security, diplomatic, military, and White House personnel.
- In addition to the 500 million e-mail accounts reported as hacked, the attackers were able to manipulate Yahoo search results to send users to spam websites after further breaching the company’s servers. In this manner, the hackers are supposed to have gained significant amounts of money. The hackers are also said to have siphoned credit and gift card details from the accounts of Yahoo users.
- Hacking Yahoo
- A tool created by a bipartisan group of national security experts and researchers to track Russian-backed online propaganda accounts – the Hamilton 68 – found that the “#fireMcMaster” hashtag became popular among these misinformation accounts at the same time that several influential users on Twitter adopted the anti-McMaster position. According to the experts, it is not the case of a political difference of opinion, but of a foreign power trying to push an agenda.
- The most recent target
- The Russians were not the only “meddlers” in the U.S. electoral process. During the 2016 presidential campaign in the U.S., the Macedonian town of Veles (population 45,000) has experienced a digital gold rush as locals launched at least 140 US politics websites with American-sounding domain names such as WorldPoliticus.com, USConservativeToday.com and USADailyPolitics.com. They almost all published fake political content, responding to straightforward economic incentives: As Facebook regularly reveals, a US Facebook user is worth about four times a user outside the US. The fraction-of-a-penny-per-click of US display advertising means considerable money in Veles. Several teens and young men who ran these sites said they learned the best way to generate traffic is to get their politics stories to spread on Facebook – and the best way to generate shares on Facebook is to publish sensationalist and often false content.
- Official and private subsequent investigations revealed that between October 2015 and May 2016, Fancy Bear used nine thousand links to attack about four thousand Gmail accounts, including targets in Ukraine, the Baltics, the United States, China, and Iran. The hacking group tried to gain access to defense ministries, embassies, and military attachés. The largest group of targets, some 40 percent, was made of current and former military personnel. Among the group’s recent breaches were the German parliament, the Italian military, the Saudi foreign ministry, the email accounts of Philip Breedlove, Colin Powell, and John Podesta, Hillary Clinton’s campaign chairman, and the DNC.
- In the DNC case, the FBI first contacted party in the fall of 2015, obliquely warning the Democrats to examine their network. It wasn’t until May 2016, however, that the DNC asked for help from a cyber-security company called CrowdStrike, which had experience identifying digital espionage operations by nation-states. CrowdStrike immediately discovered two sophisticated groups of spies that were stealing documents from the Democrats by the thousands.
- Kompromat had been deployed by the Soviet Union since at least the 1950s, but in 1999 the Kremlin gave the tactic a high-tech update. With parliamentary elections fast approaching, and with post-USSR corruption at a peak, the government of Boris Yeltsin used anonymous websites to sling mud at opposition candidates. One notorious kompromat repository was run specifically to slander the mayor of Moscow, a rising star in the opposition with his eyes on the presidency. In 2009, a senior British diplomat working in Russia was forced to resign after the appearance online of a four-minute video that showed him having sex with two blond women in a brothel. One of the American targets of kompromat was former Assistant Secretary of State for European and Eurasian Affairs Victoria Nuland, who, in February 2014, at the peak of the crisis in Ukraine, was surreptitiously recorded while speaking on the phone with the U.S. ambassador to Kiev. Frustrated with Europe’s lackluster response to the Ukrainian crisis, Nuland said, “Fuck the EU.” Shortly after, an aide to the Russian deputy prime minister tweeted a link to a recording of the intercepted phone call. The State Department called the leak “a new low in Russian tradecraft.”
- The Russians’ tactics became more sophisticated over time; they even hacked satellites to cover their tracks. Over the next two decades, the FSB (successor to the KGB) and the GRU (Russia’s premier military intelligence organization) went after political and military targets, while the NSA and the UK’s GCHQ returned the favor.
- Hacking and “kompromat”
- In the case of the so-called advanced persistent threats (APTs), great stealth is used, as well as tactics that may even affect the presidential election. One such tactic previously employed in commercial attacks by Russian hackers is code-poisoning. Hackers inject malware into a voting system manufacturer’s code. Additionally, the malware is geotagged to only target certain voting systems in certain counties across the nation. When the machines are updated, the malware silently passes to each electronic tabulator. The malware switches on when the machines are powered up on Election Day. It invisibly alters the votes and then automatically self-erases once tabulation is complete.
- In the context of the 2016 U.S. elections, the FBI investigated into breaches of elections systems in Illinois and Arizona, while an unnamed Department of Homeland Security official declared that hackers had “intensely probed” state elections systems in 20 states. Law enforcement officials have pointed the finger at Russian state-supported hackers for the attacks, a claim the Kremlin denied.
- The 2016 U.S. elections are considered to be the first grand-scale example of the threat posed by cyber-warfare (both hacking and Internet manipulation) against the 21st century political processes.
- The report also found that a social media account can become an online “celebrity” with 300,000 followers in just one month for the cost of about $2,600.
- To obtain an election outcome, a campaign operator could buy targeted news websites for about $3,000 per site and then populate the pages with propaganda that poses as legitimate news. Maintaining the sites with relevant fake content costs $5,000 a month, and targeted social media promotion costs $3,000 a month.
- With targeted spending, fake content can spark real protests. For example, campaigns can create and populate social media groups that discuss relevant ideologies for the cost of about $40,000. To maximize the reach of the content, campaigns can spend $6,000 to gain about 40,000 “high-quality” likes. Within these fake news services, it can also cost $5,000 for 20,000 comments and $2,700 for a false story. Campaigns can further buy retweets and other promotional services, such as the placement of related videos on YouTube that help the stories go viral. It can cost $10,000 to announce and promote a resulting protest on social media.
- A recent report issued by the cybersecurity firm Trend Micro titled “The Fake News Machine”[3] analyzed the costs of swaying public opinion through the spread of misinformation online. It revealed that political campaigns can manipulate elections by spending as little as $400,000 on fake news and propaganda. It also mentioned that it costs just $55,000 to discredit a journalist and $200,000 to instigate a street protest based on false news, analyzing how cyber propaganda produces real-world outcomes. The report also mentions underground marketplaces that can allow campaigns, political parties, private companies and other entities to strategically create and distribute fake content to shift public perceptions.
- Propaganda also played a key role as a recruitment tool in Russia’s military campaign against Ukraine. Within the separatist territories, Russian propaganda spurred tens of thousands of Ukrainians to take up arms against their countrymen. An enlistment office for the separatist republics was opened in Moscow for Russian citizens who wanted to join the war. And Russia’s false news reports disseminated worldwide via the internet drew foreign fighters to join Russia’s proxy army against Ukraine, including from Serbia, France, Brazil and the United States.
- As airpower did after World War I, Russia’s hybrid war against Ukraine has redefined the boundaries of the modern battlefield. Cyber-power has in part replaced many forms of traditional power, from air and submarine power to assassination. Hybrid weapons have not replaced the more tactical uses of combat airpower like close air support, or air interdiction. But hundreds of miles behind the front lines in Ukraine, Russia’s propaganda and cyber-attacks have supplanted the strategic use of airpower to affect Russia’s deep battle doctrine.
- The combined use of propaganda and cyber-warfare to support military operations on the ground are hallmarks of Russian “hybrid warfare.” In Ukraine, Russian military forces have combined World War I and II-era weapons and tactics –like artillery bombardments, tank attacks and trench warfare – with weapons unique to the 21st century battlefield, such as cyber-attacks and sophisticated propaganda campaigns geared toward TV and internet audiences. In September 2014, General Philip Breedlove, then NATO’s top commander, called Russia’s hybrid war in Ukraine “the most amazing information warfare blitzkrieg we have ever seen in the history of information warfare.”
- According to bipartisan former national security officials and researchers, the coordinated, state-backed efforts to spread disinformation during the 2016 U.S. Presidential campaign were very real, with almost 20 percent of the messages in the month before the election being originated by bots. Also, about 400,000 accounts that posted political tweets are believed to have been bots.
A cyber treaty, however, is not as simple as many seem to think. According to an independent review by the NATO-affiliated think-tank NATO Cooperative Cyber Defense Centre of Excellence, the idea of a digital Geneva Convention is “confusing and politically unrealistic.” The original Geneva Conventions are part of international humanitarian law, designed for armed conflicts and any operations that have a link to armed conflict. Attempting to take the framework outside the scope of armed conflict and make it applicable is considered an unrealistic approach offering limited options. Instead, there are other international laws accounting for peacetime cyber activities such as those found in the Council of Europe’s Convention on Cybercrime.
Conclusion: Future prospects
There is growing concern that cyberspace will become the next theater of warfare. According to some researchers, the future wars will not just be fought by soldiers or planes, they will also be fought with the click of a mouse a half a world away that unleashes carefully weaponized computer programs that disrupt or destroy critical industries like utilities, transportation, communications, and energy. Such attacks could also disable military networks that control the movement of troops, the path of jet fighters, the command and control of warships.
This has led to new terms such as cyber-warfare and cyber-terrorism. Cyber-warfare involves the battle space use and targeting of computers and networks in warfare. It involves both offensive and defensive operations pertaining to the threat of cyber-attacks, espionage and sabotage. There has been controversy over whether such operations can duly be called “war”. Nevertheless, nations have been developing their capabilities and engaged in cyber-warfare either as an aggressor, defendant, or both.
Cyber-warfare has been defined as “actions by a nation-state to penetrate another nation’s computers or networks for the purposes of causing damage or disruption”, but other definitions include non-state actors, such as terrorist groups, companies, political or ideological extremist groups, “hacktivists” and transnational criminal organizations. However, the debates continue around the term of “cyber-warfare”, with experts like Eugene Kaspersky arguing that cyber terrorism” is a more accurate term. He stated that “with today’s attacks, you are clueless about who did it or when they will strike again.” He also equated large-scale cyber weaponsto biological weapons, claiming that in an interconnected world, they have the potential to be equally destructive.
Other military experts argued that all politically motivated cyber attacks are merely sophisticated versions of sabotage, espionage, or subversion – and that it is unlikely that cyber war will occur in the future. However, while cyber-war might be, from a legal perspective, an unlikely scenario, states have to consider military-led cyber operations an attractive activity, within and without war, as they offer a large variety of cheap and risk-free options to weaken other countries and strengthen their own positions. Considered from a long-term, geostrategic perspective, cyber offensive operations can cripple whole economies, change political views, agitate conflicts within or among states, reduce their military efficiency and equalize the capacities of high-tech nations to that of low-tech nations, and use access to their critical infrastructures to blackmail them.
The speed of technological progress, and the ease with which ideas can now spread, mean that few techniques can long remain the preserve of large firms or entities. Every advance in power and convenience available to the ordinary consumer will soon be available to criminals too. Illegal commerce, whether in drugs, forged documents, stolen credit cards or emails, is nearly as slick and well organized as the legal sort. So are the criminal world’s labor exchanges: hiring someone to hack a website, or to boost a Twitter account with fake followers, is easily done. So is renting a botnet of suborned devices to knock an enemy’s website off the net.
Also, the explosion of devices connected to the net and all potentially hackable will be impossible to keep secure as new vulnerabilities are discovered. Software, like everything else, must constantly be repaired if it is not to decay.
The new kind of targeted cyber-attacks shows that cyberspace, once dominated by skilled individuals, is increasingly falling under state control, often for the benefit of these states’ own enterprises or large national corporations, and it is a worrying trend.
States have recognized the potential of hackers and have arguably employed them in pursuit of the government’s national policy and economic goals. The malicious activity in cyber-space will increasingly follow state, rather than non-state logic. This will have a deep effect on the motivations for attacks, the selection of the targets and means of attacking them. One consequence of this is that the notion of state security in cyberspace, even if only born recently, already needs to be updated.
[1] A Ponzi scheme is a fraudulent investment operation where the operator generates returns for older investors through revenue paid by new investors, rather than from legitimate business activities or profit of financial trading. The scheme is named after Charles Ponzi, an Italian swindler and con artist in the U.S. and Canada, who became notorious for using the technique in the 1920s.
[2] The name of “trolls” was coined by a Russian investigative journalist who went undercover in a pro-Putin social media commenting office in St. Petersburg in 2013. He dubbed the commentators ‘trolls’ and their office a ‘troll factory’.
[3] On 13 June 2017, see http://blog.trendmicro.com/trendlabs-security-intelligence/online-economy-fake-news/
 Eurasia Press & News
Eurasia Press & News